We assume (or hope) that today you have a well secured IT environment. All soft- and firmware are up to date, solid firewalls and antivirus keep watch over the network and numerous other measures are active... The chance that you can still become infected is minimal, but it can never be ruled out.
Firewalls and Antivirus software work largely with 'definitions' to spot known malware or attacks. However, 'Zero days' are regularly misused. These are unknown vulnerabilities in firm- and software for which no patch exists yet. These exploits are traded expensively on hacker forums. because companies can't protect themselves against it.
Hackers can now get their hands on the keys to the backdoor of thousands of organisations. Until recently, the only party that could protect you against this was the manufacturer of the hardware or software affected. But first of all, they must be aware of the leak, and secondly, they must be able (or willing) to release the budget to fix it. Then it is up to you to roll out the patch as quickly as possible.
How do you protect your environment from Zero days?
So there are -with certainty- leaks in every environment, including yours. It is just not yet known where they are and whether they are already being actively abused. Whichever way you look at it, there will come a time when unknown malware will try to take advantage of your environment in this way.
That leaves the question: How well prepared are you for this?
From infection onwards, every second counts and there are 2 things that are vital to limit the damage:
- How long does it take to detect the unknown infection?
- How soon can you prevent the infection from spreading further?
So you need a fire detection and extinguishing system to nip even brand new malware in the bud immediately. This is where Endpoint Detection & Response (EDR) can make a difference.
How can EDR detect unknown malware?
EDR operates largely as an intelligent monitoring system, supported by machine learning.
Once EDR gets to know your environment, it will send out alerts and intervene immediately when suspicious actions are detected:
- A cryptolocker that suddenly starts encrypting numerous files
- A virus that adds suspicious things to your registry or tries to embed itself in other files
- Malware that wants to abuse unused resources for the mining of cryptocurrencies
- Malware that starts scanning the network for open ports or other vulnerabilities and/or communicates with an unknown IP address.
- Even 'fileless attacks' which are otherwise almost impossible to detect because they leave no traces, come to light.
- When a program tries to remove recovery images or start irrelevant software or services
- …
In this way, EDR manages to spot and defuse even the most obscure, unknown malware almost immediately.
The suspect device is immediately quarantined to prevent further spread. The behavioral pattern of the as yet unknown malware is immediately analyzed in greater depth and trickles down to all users within the EDR ecosystem so that an even faster response can be achieved. That way, everyone is immediately protected against this new iteration of malware. Finally, EDR also tries to restore the affected workstation.
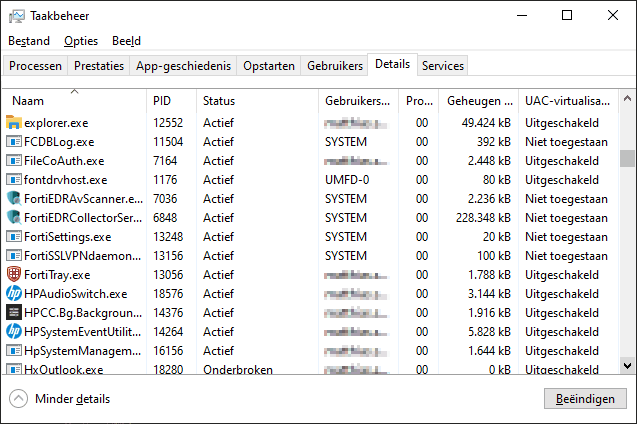
Detection, prevention, analysis and reporting
As an admin, you can keep a close eye on suspicious activities in your network via the EDR-Console. The clear dashboards not only map out any threats or suspicious movements, but also the weak points in the security of your network. Intrusion attempts are reported and in the event of a successful hack or malware infection, the affected system is blocked from the network as quickly as possible, allowing you to zoom in on the cause, the risks and the eventual recovery of the workstation or server.
How this works within FortiEDR you can see very clearly in this technical video (from 2:29)
We are happy to see that more and more organizations are discovering the way to the advanced EDR. As far as we are concerned, it is an absolute must-have within every IT environment. The advantages are numerous and obvious for any modern organization, large or small.
If you'd like more information or a demo from our experts on EDR, feel free to leave your details below and we'll arrange to meet further.
[activecampaign form=388 css=0]
share this post: