VanRoey » The Digital Workplace » Microsoft 365 » Microsoft Enterprise Mobility & Security Suite
Microsoft Enterprise Mobility & Security Suite
TAKE YOUR SECURITY TO A HIGHER LEVEL WITHOUT LIMITING MOBILITY with Microsoft Security
An employee must be able to work securely from anywhere and on any device, which poses major challenges and risks in terms of both management and security. Microsoft EMS:
is a collection of advanced management tools.
includes intelligent cloud security solutions
Gives employees one central identity
makes it easier for people to share and secure documents
Secure & manage mobile devices with Intune, MDM & MAM...
centralized identity for all
One common identity per user gives access to the on-premises Active Directory and cloud-based Azure Active Directory.
Experience the convenience of 'single sign-on' for almost all applications within your organization, not only for Microsoft Office 365 apps, but also for thousands of other popular SaaS apps.
Specific users outside your organisation (partners, external team members...) can also be subject to policies and be given access to work better together and share data.
Work securely from any device - your favorite smartphone, tablet, Mac, or PC - from anywhere, whether the device is owned by the company, the employee (BYOD), or remotely managed.
Innovative total security
With a huge amount of Microsoft security research data, take advantage of machine learning and A.I. that detects abnormalities in activity and instantly prevents threats, both on-premise and in the cloud.
Reduce the area of attack by limiting the number of confidential accounts and regularly reviewing access rights.
Enable secure file sharing internally/externally, allowing you to classify files, track their usage, and protect them anywhere. Don't allow sharing, copying, printing, and other actions, for example.
Protect your organization with single sign-on, Multi-Factor Authentication and conditional access based on user, location, device, security settings and / or applications, without affecting the authorized users.
Simplified, in-depth management
Employees get a self-service portal where they can manage passwords or PINs and access to apps and groups. They can also invite external partners to collaborate in business apps, all without the help of IT.
In one central location you can manage and consult everything, allowing you to manage all user identities, monitor updates on the status of the identity infrastructure, consult reports on user activities and audit logs.
Centrally configure all devices, policies and necessary certificates so users can easily access email, Wi-Fi, apps and their data. Their favorite devices are ready to use without having to set up much themselves.
Enjoy comprehensive app security policies, such as the ability to restrict copy/paste and save as. You don't need a device rollout and can even enforce app policies on personal devices.
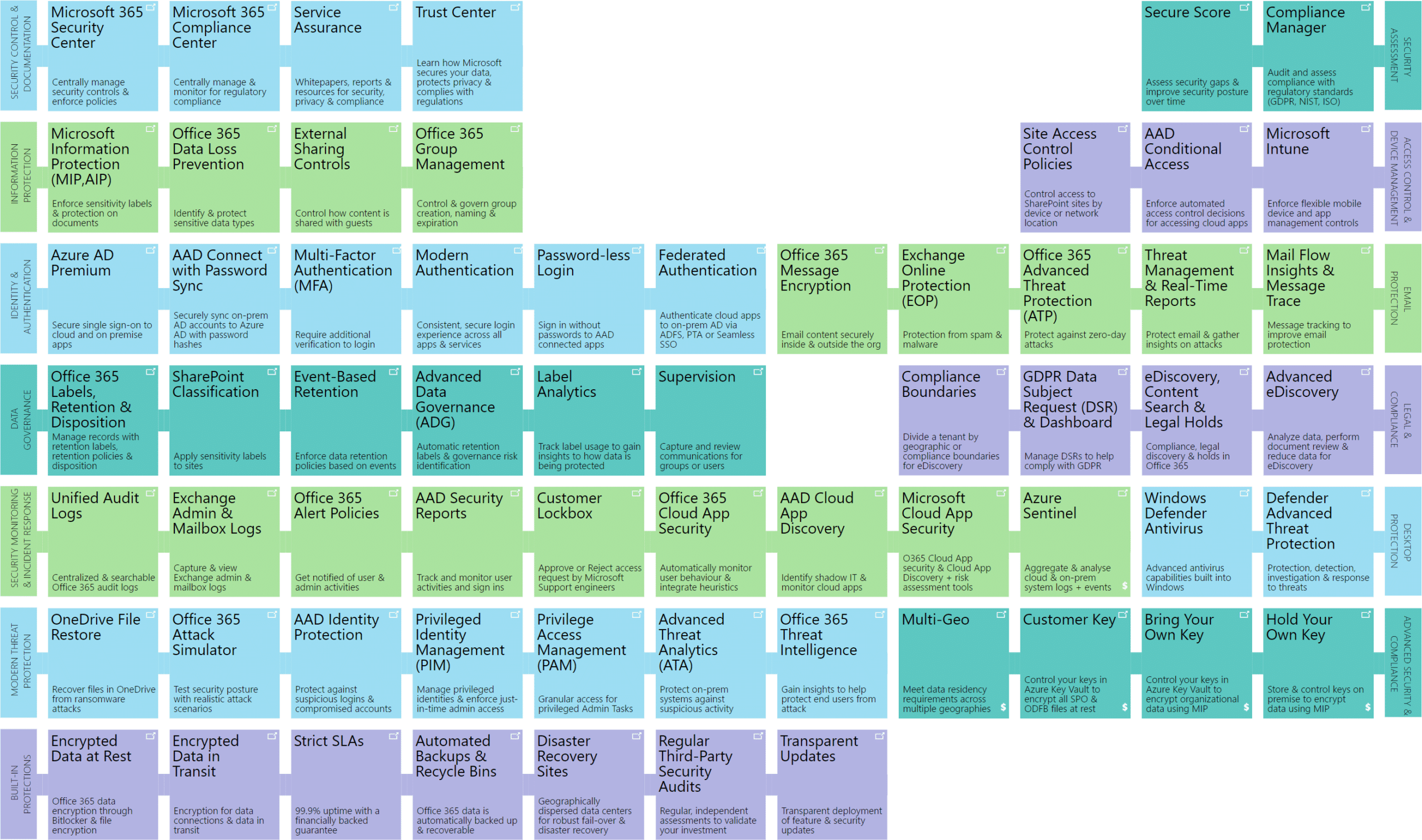
Additional information about the integrated solutions:
Enable secure mobile productivity within a BYOD environment with rock-solid Mobile Device & Application Management (MDM & MAM).
Remotely configure and manage PC deployments and let employees work extra securely with their favorite devices and apps. Set up a detailed app policy to control data access and use while maintaining the familiar Office user experience without users having to give up their devices or privacy.
In addition, Intune also offers conditional access, which can be denied or not, depending on location, behaviour, rights, device, etc. Read more about Intune at this page.
Getting started with Microsoft EMS?
Ask your question here or schedule an interview with our certified Microsoft Experts.
vat no.*
Webinar
Recently, VanRoey.be entered into a partnership with Scappman. A Belgian start-up for the automated installation & updating of third-party apps. Re-watch our webinar about Microsoft Intune here and discover the advantages of Scappman.
Overview | Enterprise Mobility + Security E3 € 9 Azure Active Directory Premium P1 | Enterprise Mobility + Security E5 € 13,9 Azure Active Directory Premium P2 |
Identity and access control | E3 | E5 |
Simplified security and access controlCentralized management of single sign-on for your devices, your data center and the cloud. | .. | .. |
Multi-Factor AuthenticationEnhance login authentication with authentication options, including notifications for phone calls, text messages, or mobile apps, and use security checks to detect inconsistencies. | .. | .. |
Conditional accessSet up contextual policies for user, location, device, and app level monitoring to grant, block, or investigate user access. | .. | .. |
Risk-based conditional accessSecure apps and important data in real time with machine learning and the Microsoft Intelligent Security Graph that lets you block access in case of risk. | .. | |
Advanced security reportingMonitor suspicious activity with reporting, auditing and alerts and resolve potential security issues with targeted recommendations. | .. | .. |
Privileged identity managementProvide timely, on-demand administrator access to online services with access-related reports and alerts. | .. | |
Windows Server Client Access License (CAL)Give each user access to server functions from multiple devices at a fixed price. | .. | .. |
Managed mobile productivity | E3 | E5 |
Mobile Device Management (MDM/MAM)With Mobile Application Management (MAM) and Mobile Device Management (MDM), register corporate and personal devices so you can implement settings and compliance, and secure corporate data. | .. | .. |
Mobile application managementPublish, configure and update mobile apps on registered and unregistered devices and secure or delete app-related corporate data. | .. | .. |
Advanced Microsoft Office 365 data protectionExpand management and security capabilities for users, devices, apps, and data while continuing to deliver a comprehensive, productive end-user experience. | .. | .. |
Integrated PC ManagementCentrally manage PCs, laptops and mobile devices from a single management console with detailed hardware and software configuration reports. | .. | .. |
Integrated on-premises managementExtend your on-premises management to the cloud with one console through the integration of Microsoft System Center Configuration Manager and Microsoft System Center Endpoint Protection for enhanced management of PCs, Macs, Unix/Linux servers and mobile devices. | .. | .. |
Information Protection | E3 | E5 |
Permanent data protectionEncrypts confidential data and sets up user rights for permanent security no matter where the data is stored or shared. | .. | .. |
Intelligent data classification and labellingConfigure policies to automatically classify and label data based on confidentiality and then apply permanent security. | .. | |
Tracking and withdrawal of documentsMonitor shared data activities and revoke access rights in the event of unexpected events. | .. | .. |
Encryption key management based on regulatory needsChoose standard key management options or implement and manage your own keys to comply with regulations. | .. | .. |
Security based on identity | E3 | E5 |
Microsoft Advanced Threat AnalyticsDetect abnormal behavior within on-premises systems and identify advanced targeted attacks and threats from within before they lead to damage. | .. | .. |
Microsoft Cloud App SecurityGain visibility, control, and protection over your cloud-based apps as well as identify threats, abnormal behavior, and other cloud security issues. | .. | |
Azure Advanced Threat ProtectionTrack and investigate advanced attacks and suspicious behavior on-premises and in the cloud. | .. |
- Recording