There are plenty of challenges as soon as you leave the work floor: Starting your accounting or ERP environment; What do you do with the telephony system? Or accessing the fileserver or the intranet... Not everything is done remotely.
VPN is no longer the way
There was a time when a VPN was the standard for teleworking. The concept is simple: Your private or work PC connects directly to your secure company network from a remote location. This makes it look as if you are on the work floor and you can access the necessary data and applications.
But people sometimes forget: the same PC, that you use outside the secure company network and maybe share with your family, is extra vulnerable to malware such as cryptolockers or viruses. So via VPN you might bring an infected device into the heart of your business environment. With all the consequences that entails.
VPN is also a threshold. The set-up for the IT department is not simple, and the configuration of each staff member is time consuming and does not always run smoothly. Not to mention connection failures and the required bandwidth for your organisation.
Then what's the way?
To prevent unprotected devices from accessing sensitive data while ensuring that everyone can use all applications effortlessly, we resort to virtualisation in the browser or via an app. In this way, you access the application or environment via a secure bubble, which your PC - regardless of the operating system - cannot influence. This can be done in 2 ways:
Application virtualization with Awingu

Windows Virtual Desktop
Inside you Microsoft 365 license you are entitled to Windows Virtual Desktop. Think of a full-fledged Windows 10 PC that runs in a secure Azure data centre, and on which you can run applications. You will then see a live stream from that desktop. It's virtually impossible for your personal or work PC to infect that virtual PC in the cloud.
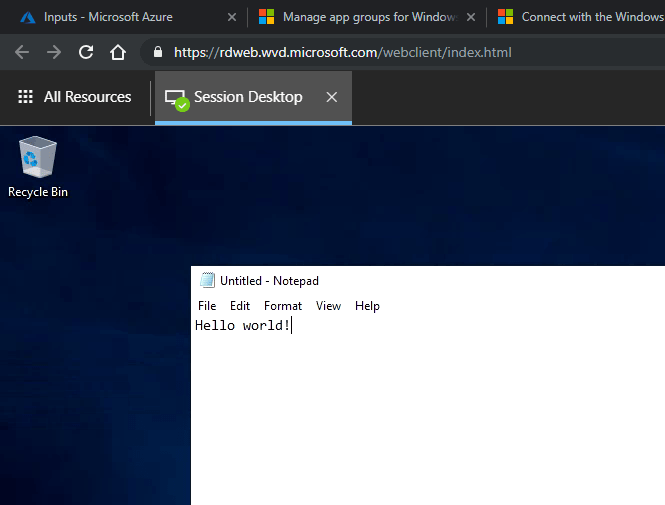
Best of all: As an organisation, you don't have to provide extra resources for this.
With services such as Cloud App Security and Conditional Access, you can therefore use your private PC to access your cloud applications without any worries, under strict conditions such as multi-factor authenticationthe right security conditions on the PC and e.g. geofencing.
What about telephony?
The landline is disappearing more and more in families. People are calling using mobile phones and apps like WhatsApp or Facebook Messenger. Organizations here are a bit more conservative and don't cut the cable right away.
A fixed number creates trust in contrast to a fleeting GSM number. In addition - thanks to call forwarding - telephones can also be received by colleagues when you are sick or busy, or outside office hours. International calls are also often cheaper from a landline.
But what if you want to work from home and still use that case number?
Fortunately, today we have the opportunity to Teams as a switchboard to use.
Teams Voice offers PBX capabilities (Private Branch Exchange) and can replace the on-premises PBX. In combination with direct routing or a call subscription, you have full call capabilities from within the app. For example, you can make and receive calls on your organisation's landline from any device, from any location.
Various functions, various situations, various wishes
There is no "one size fits all" formula when it comes to working environment. That is why it is important, especially today, to dare to take a step back and take a critical look at all colleagues:
- What are their needs?
- Which applications and files should they have access to?
- From which devices?
- Can they only do that from the office, from anywhere, or only within certain areas or timeframe?
For example, first-line workers - think of technicians or care workers on the job - must be equipped with the right security, the right equipment, the right policies... Fortunately, today it is relatively easy to define and enforce these rules thanks to Microsoft EMSBoth for certain groups of colleagues or at individual level.
The next step?
Because of Covid-19, hundreds of thousands of employees started working head-on from home. An emergency plan was worked out in full panic, but teleworking is here to stay. Today is your chance to work it out thoroughly, safely and for the future.
Feel free to speak to our colleagues via chat, business@vanroey.be or count 014 470 605 to sit together (virtually) for once. We are happy to share our experience within VanRoey.be and thousands of environments with you!