A CEO - and by extension any C-level or executive - has a certain power over his or her employees. By impersonating the CEO, cybercriminals appropriate that power by falsifying executive e-mail accounts, for example, asking employees to forward financial, confidential or business-critical data or to carry out transactions. In fact, cybercriminals with CEO fraud therefore abuse the employee's obedience.
Different targets, different tactics.
CEO fraud can be carried out in different ways: depending on the intended victim, the cybercriminal throws out a different rod...
Phishing
Phising is the well-known tactic of sending an e-mail to a large number of users. The message usually consists of A tempting financial message or a warning asking you to sign in via a link (e.g. on PayPal, your Apple account or your bank account) that will try to retrieve your login details or deliver your malware if you click on it and follow the instructions.Compare it to angling in a large fishpond with lots of fish. Every patient angler will have a bite sooner or later.
Spear Phishing
Spear phishing is a similar process but more targeted. The cybercriminal uses a spear and ejects it to one specific fish. The message contains more personalized data, which the cybercriminals collected on social media and other public channels. Unlike phishing, the chance that the victim will actually perform the requested act or transaction of money or data is much greater. Typical victims of Spear Phishing are financial, HR, IT and R&D departments. If the fake messages seem to come from your CEO, who is asking for specific information that not everyone knows you have access to, the trap is hard to see through.
Executive Whaling
Sometimes cybercriminals with CEO fraud immediately go for the fat fish, the whale. By posing as a distinguished business partner or a highly placed figure within the organization, they immediately attack the CEO himself or another manager. The objective remains the same: to extract money and valuable data. Executive Whaling is characterized by a great knowledge of the target company and the victims in person. It is therefore a time-consuming and expensive method of working for cybercriminals, which is why it mainly occurs in large, wealthy companies.
So much for fisheries. CEO fraud is also sometimes framed within a security context. Social EngineeringThis is any form of cybercrime that relies on psychological manipulation of the victims by using personal information. Collecting information about the victims on social media (also known as mining) is usually part of this.
CEO fraud therefore manifests itself in various forms. The sharp increase in the number of reports shows that this way of working is very popular among cyber criminals. Organisations that are in a strong growth phase are often the victims. New employees do not yet know the habits of their managers and are therefore less able to recognise deviant behaviour and unusual questions.
5 tips to arm yourself against CEO fraud
1. Locate the risk
By determining who and which departments within your organisation are most vulnerable, you can provide more targeted security. In addition to the managers themselves, HR, IT and Finance employees are most often targeted. In R&D intensive organisations, leading researchers are also sometimes the victims. Think like a cybercriminal. Who has access to sensitive and valuable information? Who reports directly to the CEO, to the CxO?
2. Install the basic security tools
2-Factor authentication, email filters, anti-virus software, access and authorization level management... These are some of the most essential ways to secure your IT. The investment in adequate security solutions pale in comparison to the cost of a large-scale hack or cryptolocker.
3. Implement an active security policy
Most companies have an active HR policy, which defines what is expected of their employees. To what extent is cyber security included? Large companies often have some form of security policy, but it is often very limited and seldom evolves in line with the changing techniques used by cyber criminals. In smaller organisations, an active security policy usually does not exist.
How do your people deal with e-mails from an unknown source? Is there password management? Does everyone know what the appointments are regarding WiFi access or working from home? ... Be proactive in this and set clear guidelines.
4. Simple standard procedures
A policy gives direction to the people and the organisation. Procedures ensure that the policy is maintained. However, limit the number of procedures and keep them simple. A jumble of complex procedures has a negative impact on the efficiency of your operations and will soon be rejected by the employees. Although the size of the procedures obviously depends on the size of the organisation.
For example, procedures related to information about cyber threats and their resolution make a lot of sense. Because CEO fraud attacks are usually very targeted, it is important to determine who informs you when and how. You can also provide procedures to systematically test and increase the level of security.
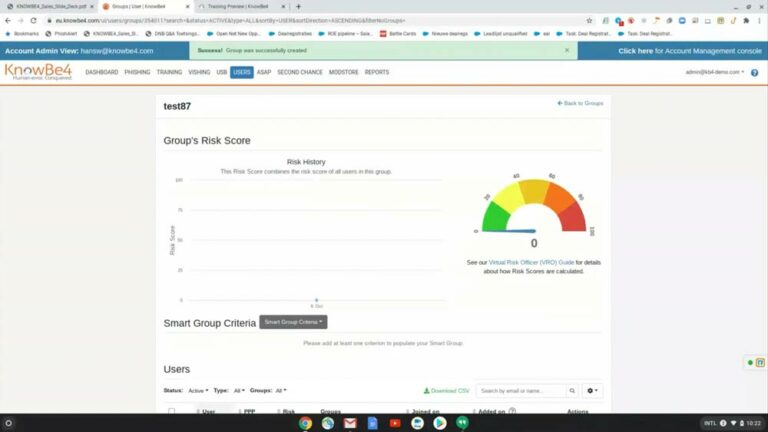
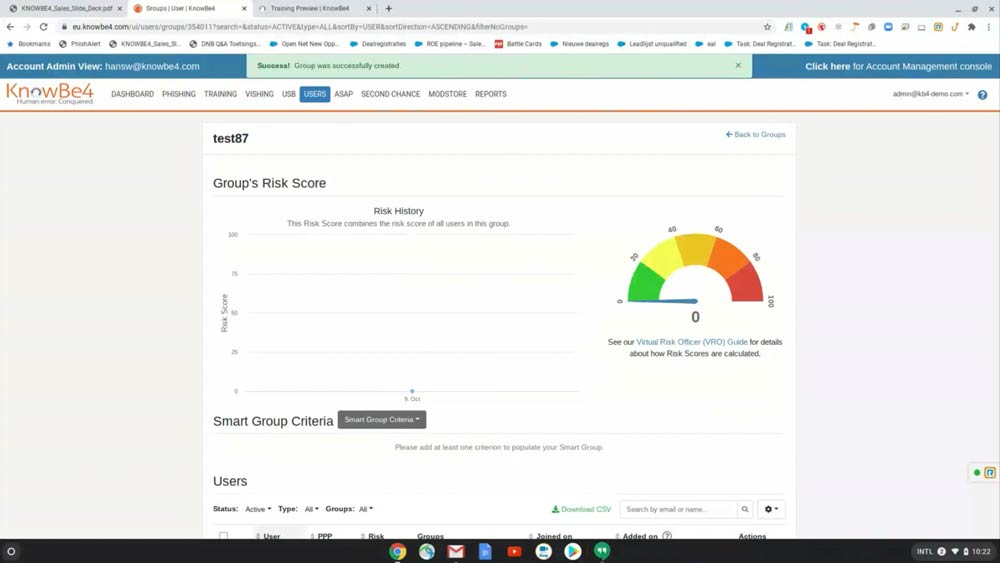
5. Security awareness training
This last tip is perhaps the most important. Making all employees aware of the threats is essential. Make sure they know what e.g. CEO fraud is, that they are aware of phishing, spear-phishing and CEO whaling. Make sure that the different risk profiles within your organisation each have their own risk. What type of attack can an HR employee expect? What type of attack can an R&D engineer expect? What information do hackers use via Social Engineering? In other words, what should you watch out for when you post something on social media, for example?
In addition, it is important that everyone knows and uses the security tools, policies and procedures. Security Awareness For your employees, this is a continuous programme with regular tests at unexpected moments.
share this post: